I have to admit that I have never really understood the PDCA concept as it applies to information security. I do know that PDCA stands for Plan-Do-Check-Act, but I have never understood the difference between Do and Act, other than there is a Check step in between. Also, I can never remember which way the wheel goes, clockwise or counter-clockwise!
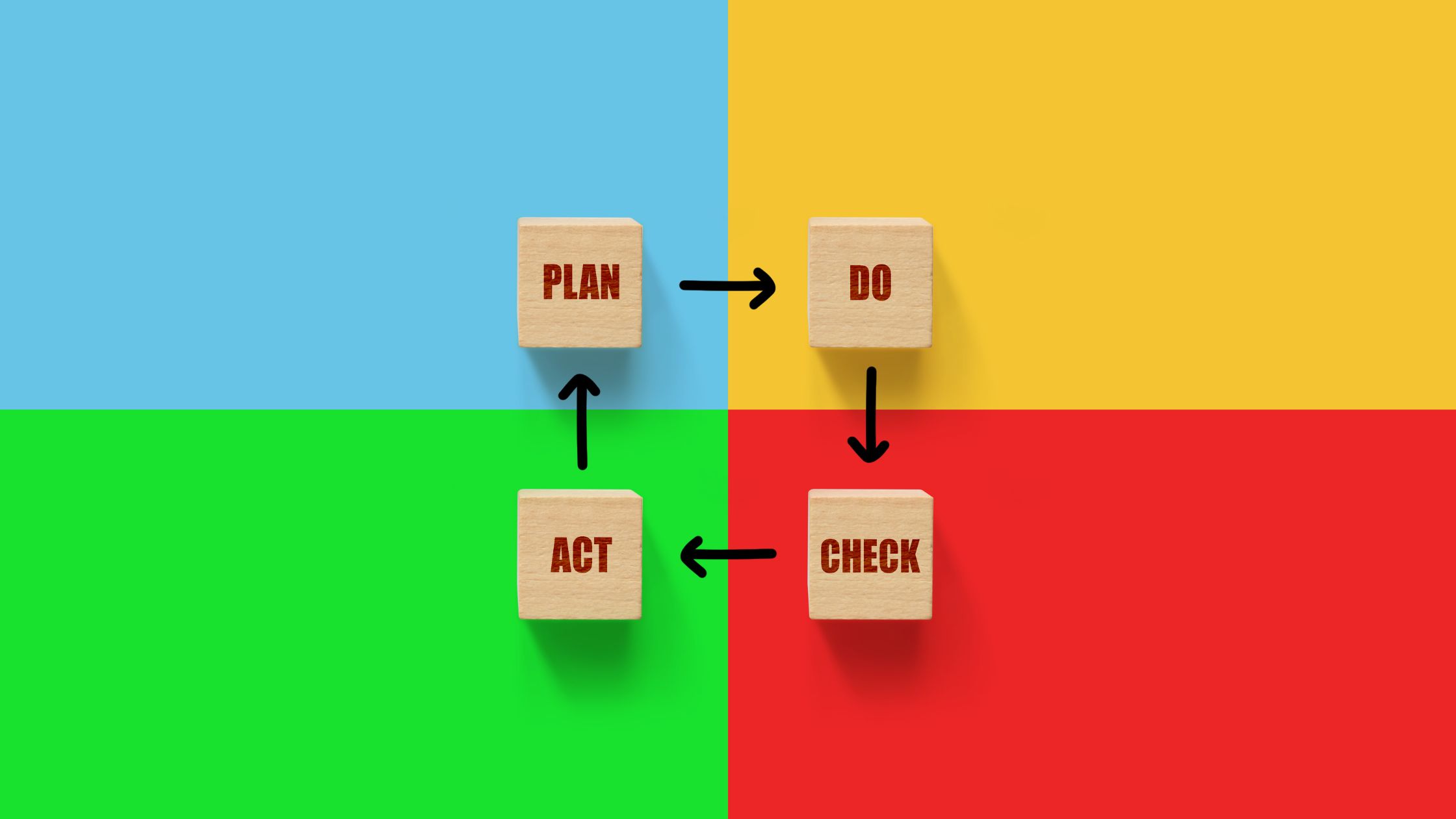
It seems like PDCA is from another era when security improvements could be regularly scheduled on an annual basis; time moved more slowly then. Now we have new types of threats on a monthly basis, or even weekly basis. We need to respond to these quickly, no matter what phase of PDCA we happen to be in at that time.
I am a big believer in continuous improvement, which I call pdca. Continuous improvement in this case refers to progress made on a daily basis and documented monthly or quarterly. This pdca is part of lean management, kaizen, etc. Unless security is managed on this basis, it will slowly degrade, until the next annual audit.
A recent article in the May, 2011 Harvard Business Review discusses these concepts in the context of motivating people. The connection to security is that fundamentally security is about people and motivating them to do the right thing. The article is “The Power of Small Wins”, by Teresa Amabile and Steven Kramer. The article presents their research, illustrating that employees are best motivated when they are able to make continuous progress in their work. This might seem obvious, but contrast with what managers think is the number one motivator: “recognition for good work”.
In short, pcda is critical to information security for two reasons: keeping up with changing threats and helping to motivate security staff, IT staff and end users to do the right thing.
Book an Appointment for Cybersecurity Issues
Request an appointment with Dr. Fred Scholl. We will discuss any cybersecurity issues you have.