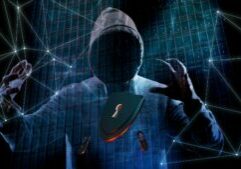
The Equifax data breach illustrates again the need for speed in security management. If the breach was through a known vulnerability, we wonder why wasn’t it patched? If through another path, we wonder why wasn’t the attack detected? We have so many incident and event management tools for servers, desktops and networks, it is hard to believe that Equifax did not have such tools. In the past, breaches like this have resulted from delays in detecting or reacting to attacks.
As the pace of digital business transformation continues to increase, security management needs to increase its rate of change. The OODA loop has been highlighted as a general approach to fast, accurate decision making. Recently I came across a really good explanation of this by John Braddock, a former CIA case officer. You can check out his book on Amazon: A Spy’s Guide to Thinking. Let’s look at what these frameworks are and how to use them in cybersecurity management.
The original OODA (Observe-Orient-Decision-Action) loop was devised by John Boyd, an Air Force pilot in the Korean War. This process was developed to help pilots prevail in combat engagements. Although Boyd did little to document his ideas, others picked them up and they have since permeated business thinking. For example, see Certain to Win, by Chet Richards, one of Boyd’s associates. They key point of the OODA loop is to minimize the time it takes to transit the loop. For cybersecurity this can be: the time to respond to an incident, the time to detect an incident, the time to patch a known vulnerability.
A Spy’s Guide to Thinking gives a very good explanation of the OODA loop; one that is better aligned with information security, not MIG pilots’ behavior. To start with, Braddock redefines the action loop as the D-A-D-A loop, or Data-Analysis-Decision-Action loop. Everyone is security starts with data, usually too much data. Analysis, decisions and actions follow. The speed we go through this process determines success or failure. Another very interesting point made by Braddock, is that the process doesn’t start with data, as in the OODA loop where fighter pilots start by observing the enemy.
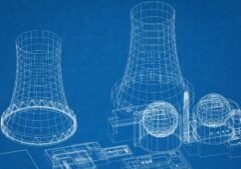
This is shown in the diagram, where the starting point is “decision”. In security we need to know what we are looking for before starting the data analysis. There’s just too much data. This includes searching for IOC’s or doing a risk analysis to decide which compliance gap to fix first.
To summarize application to effective security risk management:
- Move through the DADA process at the speed of business change
- Don’t start with data (observe); start with a framework that defines what you are looking for. This includes what the business is looking for.
Tags: Cybersecurity, Equifax data breach, Security Management
Book an Appointment for Cybersecurity Issues
Request an appointment with Dr. Fred Scholl. We will discuss any cybersecurity issues you have.