It is common knowledge that you cannot define the security of anything without understanding its context. It is also true that to improve your organization’s security posture you need to understand that organization. Over 50% of CISO’s still report to the CIO function. This blog post outlines, in Mind Map format, the activities of the CIO function and the entire IT organization. At a minimum you will be collaborating with that organization; you may well be part of it. To maximize your impact, understand the functions therein.
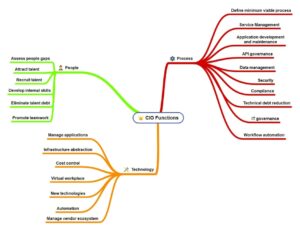
The CIO Mind Map I present is based on Mark Settle’s book Truth from the Valley (2020), in which he summarizes the functions of a modern CIO. Your organization will be different, so use this as a starting point only. CISO’s that are part of the CIO organization will likely be more security operations focused. Those outside the CIO organization will likely be more risk and governance focused.
The book opens with an extensive discussion of people issues, as shown in the diagram. This will be a focus for cybersecurity; the latest Verizon DBIR states that humans are involved with almost 80% of breaches. You need to focus on people inside the IT organization as well as business users. The second big focus area for Mark’s book is process. Without adequate process management security programs will fail. The author defines the MVP or “Minimum Viable Process”: that process needed to meet the goals of the business and IT. I like this idea better than the more rigid process maturity models that have prescriptive requirements for each level.
On the technology front cybersecurity practitioners will need to take a three-fold approach. First, protect new technologies being adopted. AI comes immediately to mind. Second, piggyback on broader scope initiatives like automation. Finally, collaborate with other teams (such as purchasing) on initiatives like vendor management.
Book an Appointment for Cybersecurity Issues
Request an appointment with Dr. Fred Scholl. We will discuss any cybersecurity issues you have.